Fortifying Business Defenses: Preparing for 2024’s Cyber-Physical Security Challenges

Introduction:
As we approach 2024, businesses are increasingly facing complex security threats that blend physical and cyber risks. From sophisticated social engineering attacks to vulnerabilities in IoT devices and the potential for insider threats, the landscape of cyber warfare demands a robust and multi-layered defensive strategy.
1. The Blurring Lines Between Physical and Cybersecurity:
The upcoming years will see a further merging of physical and cybersecurity concerns. Attacks are becoming more integrated, targeting both the physical aspects of a business, like premises and hardware, and digital assets, including data and network infrastructure.
2. Rising Threats of Social Engineering:
Social engineering attacks, which exploit human psychology rather than technological vulnerabilities, are on the rise. Businesses must train employees to recognize and respond to these threats, such as phishing, pretexting, and baiting.
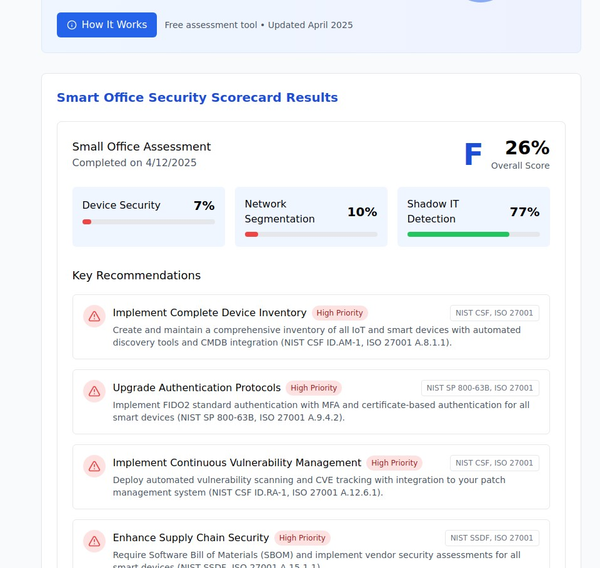
3. Securing IoT and Wi-Fi Networks:
The Internet of Things (IoT) presents a significant security challenge. As businesses increasingly rely on connected devices, securing these networks against unauthorized access and ensuring the integrity of the data they collect and transmit is crucial.
4. Insider Threats: A Persistent Risk:
Insider threats, whether intentional or accidental, remain a critical concern. Companies should enforce strict access controls, regularly audit their systems, and foster a culture of security awareness among employees.
5. Preparing for Cyber Warfare:
With the escalating intensity of cyber warfare, businesses need to adopt a proactive stance. This includes investing in advanced cybersecurity technologies, engaging in regular security training, and developing incident response plans.
6. Collaboration and Information Sharing:
Collaborating with other businesses and participating in information-sharing platforms can provide valuable insights into emerging threats and best practices for mitigation.
Conclusion:
The year 2024 is poised to bring sophisticated and integrated security challenges for businesses. By embracing a holistic approach to security, combining physical and cybersecurity measures, and fostering a culture of vigilance and collaboration, businesses can strengthen their defenses against the evolving landscape of cyber warfare.