Industrial IoT Security: Lessons from Recent Manufacturing Breaches
The convergence of operational technology (OT) and information technology (IT) has revolutionized manufacturing, but it's also created a perfect storm of security vulnerabilities. Recent breaches affecting automotive plants, food processing facilities, and pharmaceutical manufacturers have exposed critical weaknesses in Industrial IoT (IIoT) deployments—and the lessons learned apply far beyond factory floors.
This deep dive examines real-world IIoT breaches from 2024-2026, extracts actionable lessons, and provides a framework for securing industrial control systems in an increasingly connected world.
The IIoT Attack Surface: Why Manufacturing Is Prime Target Territory
Industrial environments present unique security challenges that make them particularly attractive to attackers:
Legacy Systems: Many manufacturing facilities run equipment from the 1980s-2000s that was never designed with network connectivity in mind. A 2025 study found that 64% of manufacturing facilities have at least one industrial control system (ICS) component over 15 years old.
Operational Continuity Priority: In manufacturing, uptime is everything. A minute of downtime can cost tens of thousands of dollars, creating pressure to skip security patches, delay updates, and maintain vulnerable configurations "because it works."
IT/OT Convergence Without Security: The push to connect factory floors to enterprise networks for efficiency gains often happens without adequate security architecture. Devices that controlled isolated systems are suddenly exposed to the broader internet.
High-Value Targets: Disrupting manufacturing can:
- Halt production lines (ransomware leverage)
- Steal intellectual property (process secrets, formulas)
- Cause physical damage (safety system manipulation)
- Enable corporate espionage (production schedules, costs)
- Destroy brand reputation (product contamination scares)
Case Study #1: PolymerTech Automotive Supplier Breach (August 2025)
The Incident: A tier-1 automotive parts supplier with 14 global manufacturing facilities experienced a ransomware attack that shut down production for 11 days. The attack began through a compromised IIoT predictive maintenance sensor and spread laterally through the OT network.
Attack Timeline:
Day -30: Attacker gains initial access through internet-exposed HMI (human-machine interface) with default credentials. The vendor had documented the default password in a publicly accessible PDF manual.
Days -29 to -7: Reconnaissance phase. Attackers map the network, identify critical systems, and locate backups. They discover the IT and OT networks share flat architecture with no segmentation.
Days -6 to -1: Credential harvesting and privilege escalation. Attackers compromise domain admin accounts and gain access to engineering workstations that program PLCs (programmable logic controllers).
Day 0, 2:47 AM: Ransomware deployment across 14 facilities simultaneously. Operators arrive to find HMIs displaying ransom notes. PLCs are locked with encrypted ladder logic. Safety systems remain functional but production controllers are encrypted.
Days 1-11: Production halted. Automotive OEM customers divert to other suppliers. Company attempts recovery from backups but discovers backup systems were also encrypted. Finally pays $4.7M ransom and begins recovery.
Financial Impact:
- Direct ransom: $4.7M
- Lost production: $47M
- Customer penalties: $12M
- Emergency IR/recovery: $8M
- Total: $71.7M (nearly 40% of annual profit)
Lessons Learned from PolymerTech:
1. Default Credentials Are Production Killers
The initial compromise exploited a predictive maintenance sensor system that shipped with default credentials that were never changed. The HMI interface was accessible via a public IP address for "remote diagnostics."
Actionable Takeaway:
- Inventory every IIoT device and HMI with network connectivity
- Force credential changes during installation (don't trust operators to do it later)
- Implement credential management for industrial systems (LastPass, KeePass, or industrial-specific PAM)
- Disable remote access by default; enable only when needed with VPN
2. IT/OT Network Segmentation Is Non-Negotiable
The flat network architecture allowed ransomware to jump from corporate IT to production OT. Once inside, lateral movement was trivial.
Actionable Takeaway:
- Implement Purdue Model network segmentation (or equivalent)
- Deploy industrial firewalls between IT and OT zones
- Require DMZ jump boxes for cross-zone access
- Monitor and log all IT-to-OT traffic
- Implement zero-trust principles for zone transitions
3. Backup Strategy Must Include OT Assets
PolymerTech had good IT backups but hadn't included PLC ladder logic, HMI configurations, or SCADA databases. Recovering required reprogramming from paper documents and tribal knowledge.
Actionable Takeaway:
- Backup PLC programs, HMI configurations, and SCADA databases
- Store backups offline and off-network (air-gapped)
- Test OT restoration procedures quarterly (not just IT systems)
- Maintain configuration documentation for all industrial controllers
- Version control for ladder logic and control programs
Case Study #2: FreshHarvest Food Processing Facility (January 2026)
The Incident: A food processing facility experienced a targeted attack that manipulated temperature controls in refrigeration units, resulting in spoilage of $3.2M worth of product and a temporary FDA investigation over food safety.
Attack Vector:
An industrial IoT gateway used to monitor refrigeration temperatures had a zero-day vulnerability in its web interface. The gateway was accessible from the corporate network, which had been compromised two months earlier via a phishing email.
Attack Execution:
Attackers modified temperature setpoints and disabled alarms over a 72-hour weekend period. Refrigeration units cycled between 38°F and 58°F, putting products in the "danger zone" for bacterial growth. The SCADA system logged the events but alerts were disabled.
Discovery: Monday morning quality control sampling detected elevated bacterial counts. Investigation revealed the temperature manipulation. The facility voluntarily recalled products and notified FDA.
Impact:
- Product loss: $3.2M
- Recall costs: $1.8M
- Brand reputation damage: Estimated 15% sales decline for 6 months
- FDA inspection and remediation: $400K
- Legal exposure: 3 class-action lawsuits pending
Lessons Learned from FreshHarvest:
4. Safety-Critical Systems Require Elevated Security
Temperature control in food processing directly impacts public safety. Yet it was treated like any other business process from a security perspective.
Actionable Takeaway:
- Classify IIoT systems by safety impact (food safety, personnel safety, environmental)
- Apply stricter security controls to safety-critical systems
- Implement change management for safety system modifications
- Require multi-person authentication for safety setpoint changes
- Deploy tamper detection on safety-critical sensors and controllers
5. Alarm Systems Must Be Tamper-Resistant
Attackers disabled alarms before manipulating temperatures. If alarms had triggered, the incident would have been detected within hours instead of days.
Actionable Takeaway:
- Separate alarm systems from control systems (different networks/hardware)
- Implement alarm suppression logging with manager review
- Deploy redundant alerting (SCADA + independent monitoring)
- Alert on "alarm disabled" events immediately
- Test alarm systems weekly with documented results
6. Vendor-Supplied IIoT Gateways Require Security Validation
The compromised gateway was supplied by the refrigeration equipment vendor. FreshHarvest assumed it was secure because it came from a "trusted vendor."
Actionable Takeaway:
- Security test all vendor-supplied IIoT equipment before deployment
- Require vendors to provide security documentation (pen test reports, vuln scan results)
- Include security requirements in procurement contracts
- Maintain vendor security contact list for vulnerability reporting
- Replace vendor equipment that doesn't receive security updates
Case Study #3: PharmaGenix Pharmaceutical Manufacturing (November 2025)
The Incident: A pharmaceutical manufacturer experienced intellectual property theft when attackers exfiltrated bioreactor parameters, fermentation processes, and quality control specifications for three high-value drug compounds.
Attack Details:
Nation-state actors (attributed to APT41 by incident responders) compromised a Siemens PLC controlling bioreactor processes. The PLC was connected to a SCADA system that had read-only access to the corporate network for reporting purposes.
Attackers installed custom malware on the PLC that:
- Logged process parameters every 5 seconds
- Stored data in unused memory regions
- Exfiltrated data during normal network traffic using steganography
The breach persisted for 7 months before discovery during a routine security assessment by a new CISO.
Impact:
- Trade secret loss: Valued at $200M+ (competitive advantage in biologic manufacturing)
- Competitive harm: Competitor in Asia announced similar process 4 months after breach
- Stock price decline: 18% drop when breach disclosed
- Regulatory scrutiny: FDA questioned data integrity for affected products
Lessons Learned from PharmaGenix:
7. Intellectual Property Lives in OT Systems Now
Manufacturing process parameters are often more valuable than traditional IT data. Your bioreactor settings, injection molding parameters, or chemical ratios are crown jewels.
Actionable Takeaway:
- Classify manufacturing process data as intellectual property
- Implement data loss prevention (DLP) for OT networks
- Monitor outbound data flows from OT to IT networks
- Encrypt process data at rest in SCADA databases
- Implement strict access controls for process engineers and operators
8. PLCs and Industrial Controllers Can Be Compromised
The industry assumption has been that PLCs are too obscure or simple to target. PharmaGenix proved otherwise—custom malware was written specifically for their Siemens PLCs.
Actionable Takeaway:
- Implement PLC integrity monitoring (checksums, change detection)
- Deploy allow-listing for PLC firmware and logic
- Monitor PLC CPU and memory utilization (malware leaves fingerprints)
- Restrict who can upload programs to PLCs (hardware security modules)
- Regular security assessments of PLC configurations
9. Read-Only Access Isn't Read-Only
The "read-only" connection from SCADA to IT became a bidirectional data exfiltration channel. Security controls relied on trusting the application to enforce read-only; network architecture didn't enforce it.
Actionable Takeaway:
- Enforce unidirectional data flow with hardware data diodes for sensitive OT-to-IT connections
- Don't trust application-layer "read-only" settings for security boundaries
- Deploy separate physical interfaces for data extraction
- Monitor data flow volume and patterns (exfiltration creates anomalies)
- Implement network segmentation to isolate critical OT from corporate IT
Cross-Cutting Lessons: Building IIoT Security Programs
Lesson #10: OT Visibility Is Security Foundation
You can't secure what you can't see. Many manufacturers don't have accurate inventories of connected industrial devices.
Building OT Visibility:
- Deploy passive network monitoring (Nozomi, Claroty, Dragos, Armis)
- Create and maintain asset inventory (every PLC, HMI, sensor, gateway)
- Map network architecture (trust boundaries, data flows)
- Identify vulnerabilities and EOL equipment
- Establish baseline "normal" traffic patterns
Lesson #11: Patch Management in OT Requires Different Approach
You can't just "patch and reboot" a production line during business hours.
OT Patch Management Framework:
Risk Assessment Phase:
- Evaluate vulnerability severity in context (internet-facing? safety-critical?)
- Assess exploit availability and active targeting
- Test patches in lab/staging environment (don't trust vendors blindly)
Planning Phase:
- Schedule during planned downtime or maintenance windows
- Prepare rollback procedures and backups
- Coordinate with production scheduling and quality teams
- Notify stakeholders and document change
Execution Phase:
- Implement during maintenance window
- Validate functionality before returning to production
- Monitor closely for 48 hours post-patch
- Document results and lessons learned
Compensating Controls for Unpatchable Systems:
- Network isolation
- Virtual patching (IDS/IPS rules)
- Enhanced monitoring
- Physical access controls
Lesson #12: Insider Threat and Physical Security Matter More in OT
Many IIoT breaches involve physical access or insider knowledge.
Physical Security Integration:
- Control room access controls (badge readers, logs)
- USB port locks on HMIs and engineering workstations
- CCTV monitoring of industrial control areas
- Visitor escort policies in production areas
- Secure disposal of decommissioned equipment (PLCs store programs)
Insider Threat Mitigation:
- Least privilege for control system access
- Separation of duties (one person can't modify safety systems alone)
- Logging and monitoring of all OT system changes
- Require approval for off-hours PLC programming
- Exit procedures for terminated employees (revoke access immediately)
Lesson #13: Incident Response Plans Must Cover OT Scenarios
IT incident response playbooks don't work for OT incidents. You can't just "isolate and reimage" a $2M machine.
OT Incident Response Considerations:
Unique Decision Points:
- Can we isolate without stopping production?
- Is containment worth the safety risk?
- Do we have clean backups of PLC programs?
- How do we restore without reinfection?
- When do we notify regulators (FDA, EPA, OSHA)?
OT IR Team Composition:
- OT engineers who understand the systems
- Production managers who understand business impact
- Safety officers for hazard assessment
- IT security for threat intelligence and forensics
- Legal/compliance for regulatory obligations
Pre-Stage OT IR Capabilities:
- OT forensic tools and training
- Air-gapped recovery environment for safe PLC reprogramming
- Backup PLCs, HMIs, and critical components
- Incident response retainer with OT-specialized firm
- Documented network diagrams and system interdependencies
Lesson #14: Supply Chain Risk Is OT's Biggest Challenge
Your security is only as strong as the weakest vendor-supplied component.
IIoT Supply Chain Security:
Procurement Phase:
- Security requirements in RFPs (security updates, support lifecycle)
- Vendor security assessments before purchase
- Require vulnerability disclosure processes
- Negotiate security incident notification clauses
Integration Phase:
- Security testing before production deployment
- Change default credentials during installation
- Remove unnecessary services and accounts
- Document security baseline configuration
Operations Phase:
- Monitor vendor security advisories
- Maintain vendor contact list for incident response
- Regular security reassessment of vendor equipment
- Plan replacement timeline for EOL equipment
Incident Response:
- Know who to call at 2 AM when vendor equipment is compromised
- Understand vendor's incident response capabilities and SLAs
- Have contingency plans for vendor bankruptcies or acquisition
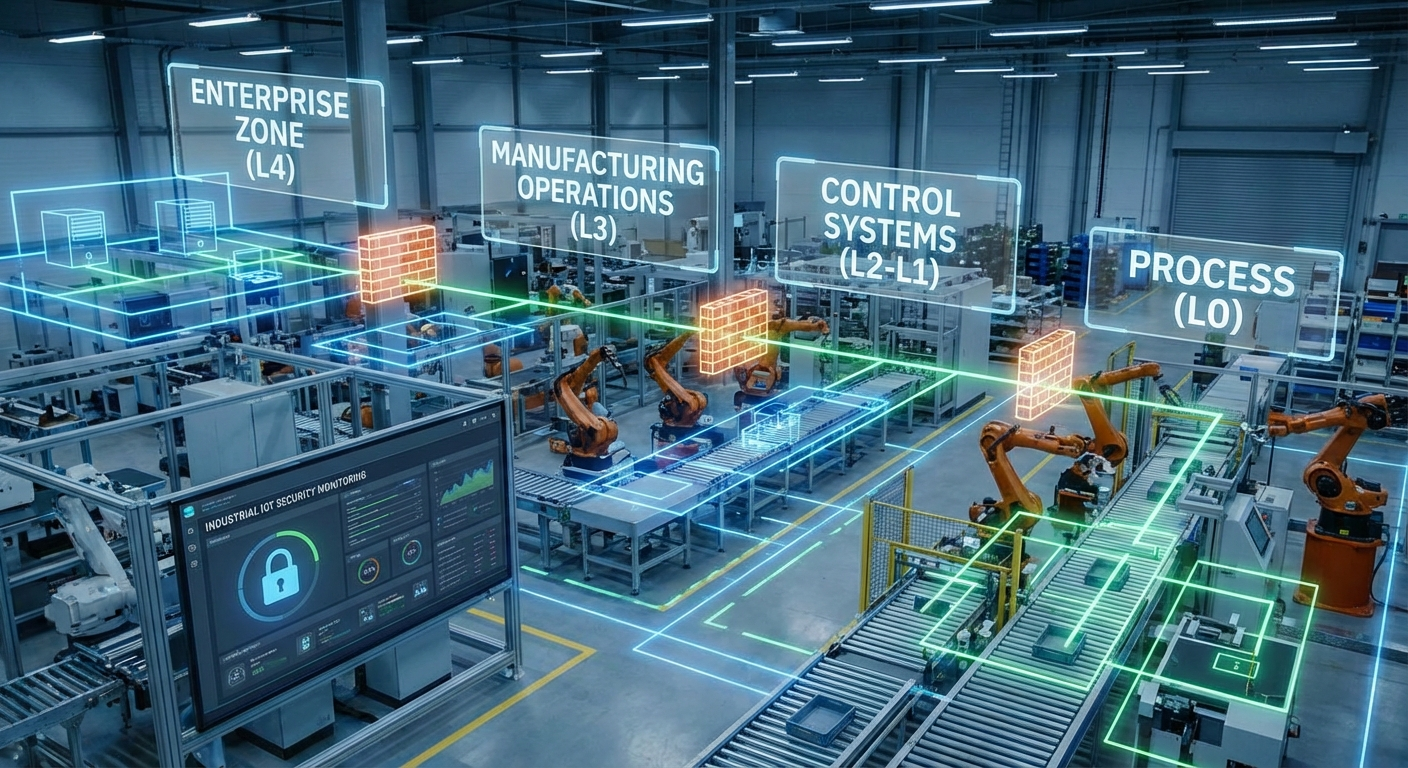
The Purdue Model: Architecture for IIoT Security
The common thread through all these breaches: inadequate network segmentation. The Purdue Model (ISA-95) provides a framework:
Level 0 (Physical Process): Sensors, actuators, physical equipment Level 1 (Basic Control): PLCs, RTUs, DCS that directly control processes Level 2 (Supervisory Control): HMIs, SCADA systems, operator interfaces Level 3 (Operations Management): MES, batch management, lab systems Level 4 (Business Logistics): ERP, scheduling, logistics Level 5 (Enterprise): Corporate IT, email, business systems
Security Zones:
- Strict segmentation between levels (firewalls, unidirectional gateways)
- Limited and monitored cross-zone traffic
- DMZ for IT-OT data exchange
- Jump boxes for remote access (never direct)
Building a Practical IIoT Security Program
Phase 1: Foundation (Months 1-3)
- Asset inventory and network mapping
- Risk assessment and criticality classification
- Establish baseline security controls (change default credentials, disable unnecessary services)
- Deploy passive monitoring for visibility
Phase 2: Quick Wins (Months 3-6)
- Implement network segmentation (at minimum: IT-OT separation)
- Establish backup and recovery for OT assets
- Develop OT incident response plan
- Vulnerability assessment of internet-facing systems
Phase 3: Maturation (Months 6-12)
- Deploy industrial IDS/IPS
- Implement access management and MFA
- Establish patch management program
- Conduct tabletop exercises and red team assessments
Phase 4: Optimization (Year 2+)
- Continuous monitoring and threat hunting
- Security automation and orchestration
- Integration with corporate SOC
- Regular security assessments and audits
Metrics That Matter for IIoT Security
Technical Metrics:
- % of OT assets with current inventory
- Mean time to detect (MTTD) anomalies in OT environment
- % of internet-facing ICS with multi-factor authentication
- Patching coverage for patchable OT systems
- Number of unmitigated critical vulnerabilities
Business Metrics:
- Cost of OT security incidents (downtime + recovery)
- Insurance premium changes (cyber insurance increasingly covers OT)
- Customer audit findings (automotive and pharma customers audit suppliers)
- Regulatory compliance status (FDA, NERC-CIP, etc.)
The Road Ahead: IIoT Security in 2026 and Beyond
Emerging Threats:
- AI-powered attacks that learn normal production patterns and hide within them
- Supply chain compromises of ICS vendors and component manufacturers
- Ransomware groups targeting specific industries (food, pharma, automotive) with tailored attacks
- Nation-state actors using OT access for geopolitical leverage
Technology Evolution:
- Zero-trust architecture for OT environments
- Blockchain for supply chain integrity
- AI/ML for anomaly detection in industrial processes
- Quantum-resistant cryptography for long-lived industrial systems
Regulatory Pressure:
- Mandatory ICS security standards (similar to NERC-CIP expanding to other sectors)
- Incident reporting requirements for critical manufacturing
- Supply chain security requirements
- Cyber insurance requirements driving baseline security
Conclusion: Security as a Production Requirement
The breaches examined here share a common theme: security was treated as an afterthought to production efficiency. In 2026, that's no longer viable. Cyber attacks cause physical shutdowns, product contamination, and intellectual property theft at scales that threaten business viability.
The manufacturing mindset shift required:
- Security is a production requirement, not an IT concern
- Downtime from poor security exceeds downtime from security measures
- OT security is a competitive advantage (customers increasingly audit it)
- Investment in IIoT security has ROI measured in avoided incidents
Start with these five actions this month:
- Inventory your IIoT devices - You can't secure what you don't know exists
- Segment IT from OT - Flat networks are indefensible
- Change default credentials - Low-hanging fruit for attackers
- Backup PLC programs - Recovery requires more than IT backups
- Deploy OT monitoring - Visibility is the foundation of security
The convergence of IT and OT brought tremendous efficiency gains to manufacturing. Securing that convergence is the challenge of this decade. The manufacturers who treat IIoT security as a core operational competency will thrive. Those who don't will appear in future breach case studies.
The question isn't whether your IIoT environment will be targeted—it's whether you'll be ready when it happens.





