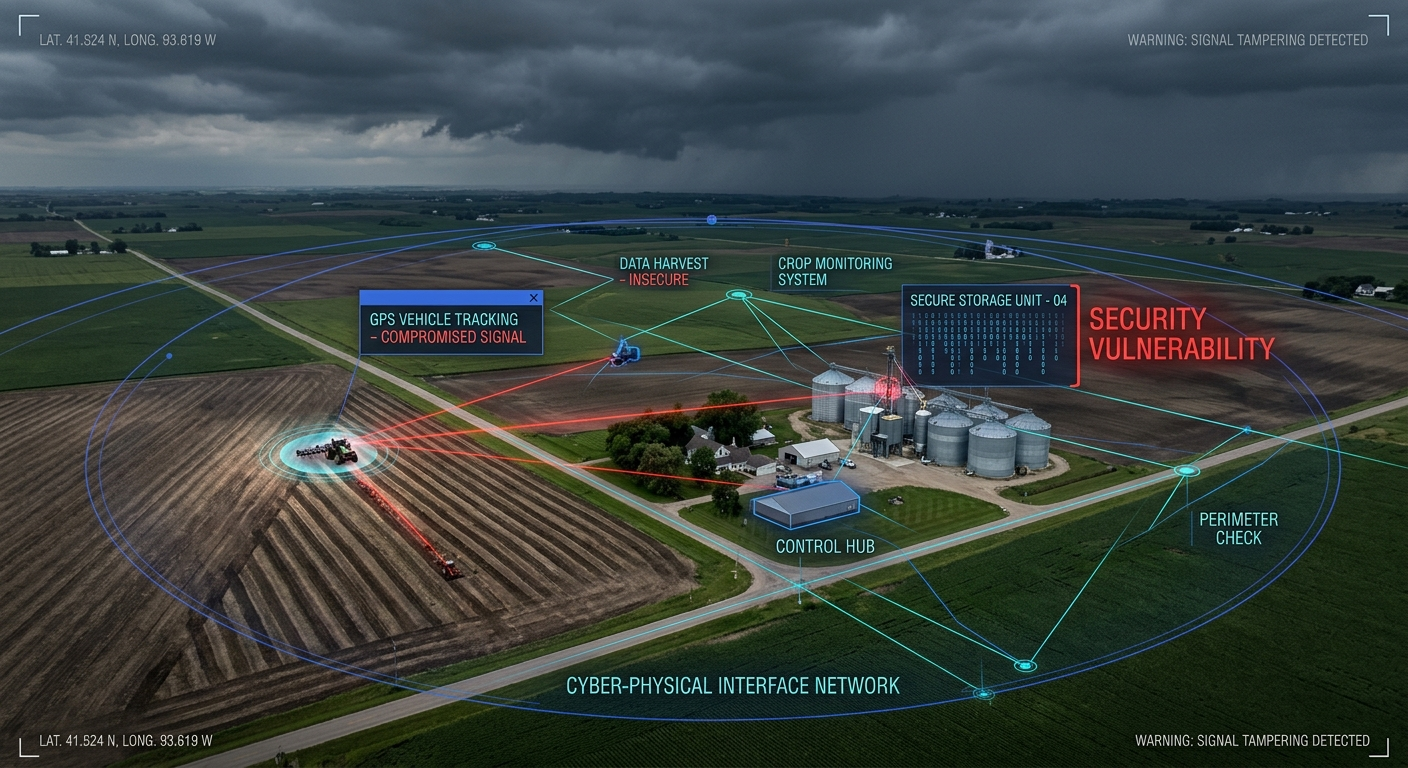
Shadow AI Is Your Biggest Unmanaged IoT Problem — And 76% of Organizations Already Have It
Shadow AI has surged to 76% of organizations in 2026, up from 61% a year ago. AI agents now autonomously control IoT devices, access operational systems, and make decisions without security oversight. The result is a new category of unmanaged attack surface that most enterprise security teams aren't equipped to handle.